Security and Compliance
The security of our clients, our candidates, and our tests is a top priority at Criteria. Learn why more than 4,000 organizations trust Criteria to help them maximize their talent success.

Trust Center
Information Security
The security of our clients, our candidates, and our tests is a top priority at Criteria. To ensure this, we focus on maintaining and investing in the latest advancements in secure technology. We aim to make the Criteria platform as secure as possible – without sacrificing performance or detracting from the user experience.
Our security program is based on resiliency and limited trust principles. In other words, we:
- Use federated services for managing user access and rights
- Use a Secure Software Development Life Cycle (SDLC) aligned with OWASP and usage of DAST and SAST for our code reviews
- Don’t allow BYOD (bring your own device)
- Conduct a comprehensive staff security training program.
To provide our customers with the level of security they expect, we have adopted ISO27001:2022 as our information security management system. With this system in place, you can trust that we will protect your data with the utmost security, above and beyond a compliance initiative.
End-to-End Security
The Criteria platform is hosted entirely on Amazon Web Services (AWS), which boasts robust built-in privacy features and provides end-to-end security. To learn more about AWS security and its features, head to https://aws.amazon.com/security/. AWS is certified SOC 2 Type 2, meaning that they are regularly audited and tested to meet these high security standards.
Criteria customer data is hosted by AWS in secure data centers around the globe. AWS maintains an impressive number of reports, certifications, and third-party assessments to preserve their state-of-the-art data center security.
Data Security
Your data is housed in tightly-controlled data centers around the world, leveraging both technological security and physical controls to prevent unauthorized access and keep your information safe and secure at all times.
Application Security
The Criteria data ecosystem is continuously monitored to maintain a high standard of security, availability, and performance that you can rely on. We have automated security testing and use third party penetration testing to stay ahead of potential threats to your data.
All data at Criteria is encrypted at rest using AES-256 encryption and the latest TLS encryption for data in flight.
Technology You Can Trust
We are committed to modern technology, and are always seeking to match the latest and greatest advancements in tech. This commitment allows Criteria’s platform to be highly scalable, stable, and secure.
Scalability
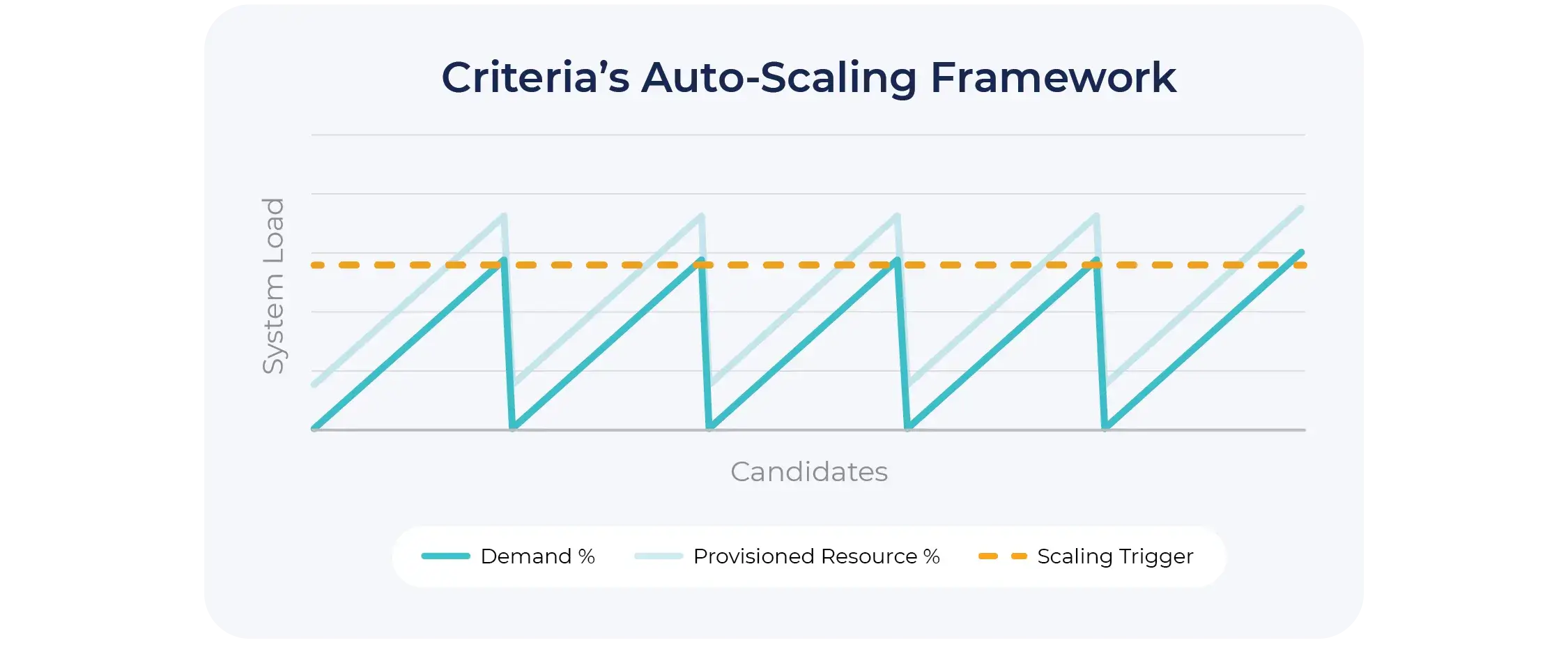
The cloud-based nature of our platform makes it possible to increase platform capacity as needed. We employ auto-scaling best practices along with significant investment in serverless technologies to remain on the bleeding edge. This elastic expansion ensures that our servers will never hit capacity and can scale to meet ever-increasing demand.
Since our infrastructure expands dynamically as needed, we are able to support your data needs, regardless of their size or complexity.
Stability
The Criteria platform is highly scalable in a highly secure way. We utilize end-to-end encryption, where information is encrypted both at rest and in transit to ensure its protection.
Our infinite scalability enables our stability. Since our infrastructure dynamically updates and scales to meet demand, our application is reliable and redundant under stress, meaning that it won’t crash or fail to meet your needs.
Security
We take security seriously. Our stability, scalability, and commitment to implementing cutting edge security practices protect your data. Along with our vast technical controls, every Criteria employee is trained and held to the same rigorous security practices to prevent data breaches and keep your information safe.
Test Security
Our commitment to security extends beyond how we maintain our platform – we keep our tests just as secure. We use dynamic testing to mitigate the risk of cheating, employ adaptive testing techniques, and can flag inconsistencies in responses.
Visit Criteria’s Test Security page to learn more.

Need more information?
If you'd like to see more detailed information, believe you have found a vulnerability, or have any other security concern, please reach out to us at security@criteriacorp.com.
Compliance
Criteria is compliant with the following regulations:Read Criteria’s full Data Processing Addendum to learn how we process and handle your data.
ISO Certified and SOC 2 Type II Compliant

Privacy
Criteria embraces privacy from the ground up by building our products to adhere to design principles that better enable us to protect your data. Our approach to personally identifiable information is to collect only the minimal amount to provide our service.
We implement the following privacy principles
- Lawfulness, fairness, and transparency
- Purpose limitation
- Data minimization
- Accuracy
- Storage limitation
- Integrity and confidentiality
- Accountability
You can read our privacy policy here.
Documentation
Visit Criteria’s Trust Center to access documentation related to security, compliance, legal, and business policy.












